nvd_feed_api
A simple ruby API/library for managing NVD CVE feeds. The API will help you to download and manage NVD Data Feeds, search for CVEs, build your vulnerability assessment platform or vulnerability database.
nvd_feed_api
A simple ruby API/library for managing NVD CVE feeds. The API will help you to download and manage NVD Data Feeds, search for CVEs, build your vulnerability assessment platform or vulnerability database.

RABID
A CLI tool and library allowing to simply decode all kind of BigIP cookies.

ctf-party
A library to enhance and speed up script/exploit writing for CTF players (or security researchers, bug bounty hunters, pentesters but mostly focused on CTF) by patching the String class to add a short syntax of usual code patterns.
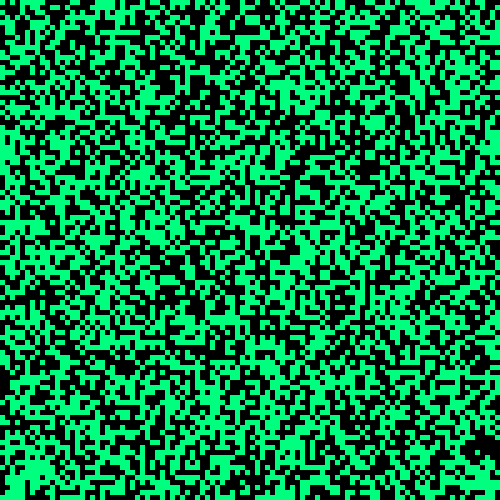
PixelChart
Map binary data into a beautiful chart.

Pass Station
CLI & library to search for default credentials among thousands of Products / Vendors.

TLS map
CLI & library for mapping TLS cipher algorithm names: IANA, OpenSSL, GnuTLS, NSS.

kh2hc
Convert OpenSSH known_hosts file hashed with HashKnownHosts to hashes crackable by Hashcat.

unisec
Toolkit for security research manipulating Unicode: confusables, homoglyphs, hexdump, code point, UTF-8, UTF-16, UTF-32, properties, regexp search, size, grapheme, surrogates, version, ICU, CLDR, UCD, BiDi, normalization, etc.

AD Assault
An Active Directory environments pentest tool complementary to existing ones like NetExec.

quartz-utils
Everyday CLI utilities that are easily pipable. url2host, stripansi, crlf2lf, lf2crlf, etc.

ChronoLeak
ICMP Timestamp Remote Time Leaker.
Flask Session Cookie Decoder/Encoder
A simple python script that let you encode and decode a Flask session cookie.

HAITI
Hash type identifier (CLI & lib).
itdis
Is a small tool that allows you to check if a list of domains you have been provided is in the scope of your pentest or not.

VBSmin
VBScript minifier CLI tool and library
vrt-cli
A simple tool to visualize VRT (Vulnerability Rating Taxonomy) from the CLI.

BQM
Deduplicate custom BloudHound queries from different datasets and merge them in one customqueries.json file.

miniss
Displays a list of open listening sockets. It is a minimal alternative to ss or netstat to offer a static binary that can be deployed on containers or hardened environnement where the classical binaries have been removed.

hivexcavator
Extracting the contents of Microsoft Windows Registry (hive) and display it as a colorful tree but mainly focused on parsing BCD files to extract WIM files path for PXE attacks.

AspiSec
Vacuuming out the remnants of offensive tools. AspiSec is responsible for removing the traces and confidential information left by offensive security tools on an auditor's computer in various cache and log files.

php-serialized-formatter (psf)
PHP serialization library that can parse and generate PHP's serialization format including PHP sessions specific format. The CLI tool can unserialize PHP objects or sessions from a string or a file to a pretty hash, JSON (minified or pretty) or YAML.
Umbraco RCE
Umbraco CMS 7.12.4 - (Authenticated) Remote Code Execution
OpenEMR RCE
OpenEMR <= 5.0.1 - (Authenticated) Remote Code Execution
Fuel CMS RCE
Fuel CMS 1.4 - Remote Code Execution
OpenNetAdmin RCE
OpenNetAdmin 8.5.14 <= 18.1.1 - Remote Command Execution
OpenEMR CVE-2019-14530
OpenEMR < 5.0.2 - (Authenticated) Path Traversal - Local File Disclosure
Easy!Appointments CVE-2022-0482
Easy!Appointments < 1.4.3 - Unauthenticated PII (events) disclosure
Joomla! CVE-2023-23752
Joomla! < 4.2.8 - Unauthenticated information disclosure
ScriptCase Pre-Auth RCE
Chaining administrator's password reset (authentication bypass, CVE-2025-47227) and shell injection (authenticated remote command execution, CVE-2025-47228)
AtMail Exploit toolchain
AtMail Email Server Appliance 6.4 - Exploit toolchain (XSS > CSRF > RCE)
Bludit Auth BF mitigation bypass
Bludit <= 3.9.2 - Authentication Bruteforce Mitigation Bypass
CMSUno RCE
CMSUno 1.6.1 <= 1.6.2 - Remote Code Execution (Authenticated)
Monitorr exploit toolkit
Multiple exploits for Monitorr (unsecure file upload, authorization bypass, technical information leakage)
OpenEMR CVE-2018-15139
OpenEMR < 5.0.1.4 - (Authenticated) File upload - Remote command execution
iTop CVE-2022-24780
iTop < 2.7.6 - (Authenticated) Remote command execution
Kirby XXE CVE-2023-38490
Kirby < 3.9.6 XML External Entity
Offensive Security Exam Report Template in Markdown
Markdown Templates for Offensive Security OSCP, OSWE, OSCE, OSEE, OSWP exam report.
Bug Bounty légal en FRANCE [FR]
Quelques conseils autour des obligations légales, fiscales et juridique pour la pratique du Bug Bounty en France
EntroCalc [FR]
Calculateur d'entropie de mot de passe.
Chromium addon | ArchLinux Search
A Chromium-based browser extension that adds ArchLinux as a search engine with an Omnibox keyword.
XSS classification model
XSS classification model - Types of Cross-Site Scripting
ACCEIS Vulnerable Code Snippets
Vulnerable code snippets repository showcasing different vulnerabilities to practice code analysis skills.
Firefox addon | ArchLinux Search
A set of Web Extensions that adds ArchLinux (bug tracker, forum, packages, wiki, AUR) as a search engine to the Firefox browser.
Bitmap
TheBlackSide challenge: image steganography
Red Stone One Carat
TryHackMe room: First room of the Red Stone series. Hack ruby using ruby.
Men in black box
A web challenge that was available during SigSegV1 CTF (2018). It was a Boolean-based Blind SQLi with WAF.
Fat
A web challenge that was available during SigSegV2 CTF (2019). It was a Slim SSTI combined with a Sinatra/Rack session cookie forgery.
Image Checker 2
A web challenge that was available during SigSegV2 CTF (2019). It was a XXE OOB via SVG combined with a SSRF port scan and a SSRF localhost bypass.
Une porte peut en cacher une autre
A web challenge that was available during SigSegV2 CTF (2019). It was a b374k.php webshell with c99 style PHP backdoor authentication bypass.
The long way
A misc challenge that was available during SigSegV2 CTF (2019). It was a extra long file path on exFAT FS, scripting was mandatory to retrieve the whole path.
Matz 2.3
A reverse challenge that was available during SigSegV2 CTF (2019). Ruby bytecode reverse engineering/disassembly making use of RubyVM class.
ffuf
TryHackMe room: (Walkthrough) Enumeration, fuzzing, and directory brute forcing using ffuf.
Crack The Hash Level 2
TryHackMe room: Advanced cracking hashes challenges and wordlist generation.
Sensory Domination Droid
A programming challenge that was available during SigSegV1 CTF (2018). It was an IRC bot, the goal was to parse private IRC messages.
Image Checker 1
A web challenge that was available during SigSegV2 CTF (2019). It was a XXE OOB via SVG rasterization and a local file read.
10 questions about my system
A forensics challenge that was available during SigSegV2 CTF (2019). It was a Volatility profile creation and 10 basic questions on the memory dump.
noraj secret zone
A web/misc/reverse/network challenge that was available during SigSegV2 CTF (2019). It was an eepsite (I2P website) containing obfuscated JavaScript.
Drugs: crack & hash
A cracking challenge that was available during SigSegV2 CTF (2019). Password hash cracking with custom dictionary/wordlist. There were 10 hashes to crack.